SOC 2 Compliance Guide for Startups: Passing Data Security Audits in 2026
In 2026, enterprise buyers don’t take your word for security anymore.
Procurement teams have one simple rule now: no SOC 2 report, no contract.
That’s the reality for startups selling into the enterprise market. Whether you’re building an AI platform or scaling a SaaS product, large customers expect proof—not promises. And the proof comes in the form of a SOC 2 report (System and Organization Controls 2).
But here’s where many founders misunderstand the process. SOC 2 isn’t just another compliance checkbox. Done right, it becomes a trust signal that shortens sales cycles and removes security objections before they even show up.
When a SOC 2 audit is completed, an independent auditor confirms that your internal security controls meet the standards defined by the American Institute of Certified Public Accountants (AICPA). For enterprise buyers, that external validation matters.
In practical terms? SOC 2 doesn’t just protect your systems—it helps close deals.
Understanding the Five SOC 2 Trust Services Criteria
Startups often approach SOC 2 the wrong way. They assume they must cover everything from day one.
You don’t.
SOC 2 is built around five Trust Services Criteria (TSC), and you only need to include the ones that match your service commitments and risk profile.

Trying to implement all five immediately usually slows teams down and increases audit costs.
A more strategic approach works better.
- Security (The Foundation of SOC 2)
Every SOC 2 audit includes the Security criterion. No exceptions.
This category focuses on protecting systems and data from unauthorized access, disclosure, or damage.
Auditors typically review controls like:
- Multi-factor authentication (MFA)
- Network firewalls
- Intrusion detection systems
- Endpoint protection tools
- Access monitoring
The real question auditors ask is simple: Who can access your systems, and how is that access controlled?
If access controls are weak, nothing else matters.
- Availability
Availability asks a straightforward question: Will your service still run when customers need it?
For infrastructure providers, cloud platforms, and mission-critical SaaS products, uptime becomes a major concern.
Auditors will look at areas such as:
- Disaster recovery testing
- Backup strategies
- Incident response procedures
- Redundant system architecture
It’s not enough to say you have backups. You need evidence that those backups actually work.
- Processing Integrity
Processing Integrity focuses on whether systems produce accurate, complete, and timely results.
This criterion is particularly relevant for:
- Fintech platforms
- Data analytics tools
- Payment systems
- Automated decision engines
Controls usually include:
- Error detection mechanisms
- Data validation rules
- QA testing procedures
- Processing logs
If your platform processes financial transactions or business-critical data, this category becomes extremely important.
- Confidentiality
Confidentiality addresses something enterprise customers care deeply about: who can see sensitive data.
If your startup handles proprietary information, internal documents, or customer datasets, this criterion quickly becomes essential.
Typical controls include:
- Encryption for data in transit
- Encryption for data at rest
- Role-based access control (RBAC)
- Least-privilege access policies
In other words, access must be intentional and limited. Random permissions scattered across the system will raise red flags immediately.
- Privacy
Privacy is often confused with confidentiality, but they focus on different things.
Confidentiality protects sensitive business information. Privacy focuses on Personally Identifiable Information (PII).
Examples include:
- Names
- Email addresses
- Social security numbers
- Health records
If your product collects or processes personal data, auditors will expect controls around:
- Data retention policies
- Consent management
- Privacy disclosures
- Data handling procedures
Privacy requirements often overlap with global regulations like GDPR or CCPA, so many companies choose to include this criterion when user data is involved.
Practical Advice for AI and SaaS Startups
Most early-stage tech companies don’t need all five criteria immediately.
A common starting combination is:
Security + Confidentiality + Availability
For AI startups in particular, Confidentiality tends to matter the most. Enterprise customers want reassurance that their data isn’t being exposed during model training or system operations.
Ignore that concern, and deals start stalling.
SOC 2 Type 1 vs. Type 2: What’s the Difference?
Another question founders ask early: Should we pursue SOC 2 Type 1 or Type 2 first?
Understanding the distinction helps control SOC 2 audit costs in 2026.
SOC 2 Type 1
A Type 1 report evaluates whether your security controls are designed properly.
Think of it as a snapshot in time. Auditors review your documentation, system configuration, and control framework at a specific moment.
Typical details:
- Timeline: 1–2 months
- Cost: $5,000 to $20,000
- Goal: demonstrate that controls exist
Type 1 reports often help startups unblock enterprise conversations quickly. Buyers see that a formal security program is already in place.
But it’s only the first step.
SOC 2 Type 2
A Type 2 report goes much deeper.
Instead of reviewing a single moment, auditors observe your controls over a period of three to twelve months.
They look for consistency:
- Was MFA always enabled?
- Were access reviews performed regularly?
- Were terminated employees removed from systems quickly?
The difference is huge.
Type 1 shows you designed the rules. Type 2 proves you actually follow them.
Typical numbers:
- Timeline: 6–12 months
- Cost: $15,000 to $50,000+
Most enterprise contracts now require vendors to obtain a Type 2 report within the first year of doing business.
Compliance Automation: Vanta vs Drata
Not long ago, SOC 2 preparation involved endless spreadsheets and screenshots.
Security teams manually gathered evidence for every control—system logs, user access lists, configuration files. It was slow and painful.
That process has largely disappeared.
Modern compliance automation platforms now handle much of the heavy lifting.
Two tools dominate the startup market: Vanta and Drata.
Vanta
Vanta became popular because it’s easy to deploy.
The platform connects directly to tools many startups already use:
- AWS, Azure, or Google Cloud
- GitHub
- Google Workspace
- Okta
Once integrated, Vanta continuously checks system configurations and collects evidence required for SOC 2 controls.
For early-stage companies trying to move quickly, that simplicity matters.
Drata
Drata targets organizations with more complex environments.
It offers:
- deeper control customization
- advanced monitoring capabilities
- better support for multi-entity infrastructures
Engineering-heavy teams often prefer Drata because they can map controls more precisely across different systems.
One Important Reality Check
Automation tools simplify compliance work, but they do not replace the audit.
An independent CPA firm must still review your controls and issue the official SOC 2 report.
Think of automation platforms as the evidence engine.
The auditor is the final authority.
How Startups Prepare for a SOC 2 Audit
If you’re wondering how startups actually obtain SOC 2 certification without overwhelming their teams, the process usually follows five stages.
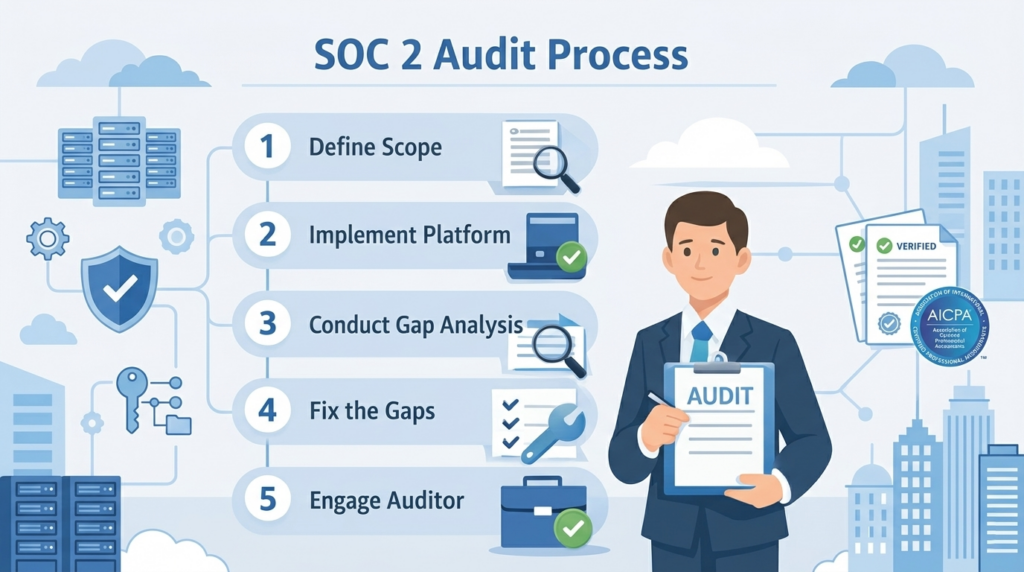
- Define the Audit Scope
Start by identifying which systems store or process customer data.
Then decide which Trust Services Criteria apply.
A narrow, well-defined scope makes the entire audit faster and cheaper.
- Implement a Compliance Platform
Most companies adopt tools like Vanta or Drata to integrate with their infrastructure.
Typical integrations include:
- cloud providers
- identity management systems
- code repositories
This connection allows the platform to continuously monitor security controls.
- Conduct a Gap Analysis
Once the system scans your environment, weaknesses become obvious.
Common issues include:
- missing multi-factor authentication
- undocumented access policies
- incomplete employee offboarding processes
This stage reveals how far you are from compliance.
Sometimes the gap is small. Sometimes it’s not.
- Fix the Gaps
This is where the real work happens.
Teams must:
- write security policies
- implement access controls
- configure monitoring systems
- establish employee onboarding and offboarding procedures
For most startups, remediation takes several months.
- Engage an Independent Auditor
Finally, a licensed CPA firm reviews your controls and supporting evidence.
Choosing an auditor familiar with your compliance platform can make the process significantly smoother.
Evidence flows directly from the automation system to the audit team, reducing back-and-forth requests.
Why SOC 2 Matters More Than Ever
SOC 2 isn’t just a document you send to customers.
It reflects how seriously your organization treats security.
When your systems enforce strong access controls, when logs are monitored continuously, when data handling policies are actually followed—customers notice.
And procurement teams notice even faster.
The companies that succeed in enterprise markets are rarely the ones with the most features. They’re the ones buyers trust.
SOC 2 is one of the clearest ways to demonstrate that trust.
And once the framework is in place, your team can stay focused on building great products while maintaining an always-audit-ready security posture.
That’s the real goal. Not just passing the audit.
Building a security program that grows with your company.
