Choosing the Right Managed Service Provider for Law Firm IT Security in 2026
Law firms have quietly become one of the most attractive targets for cybercriminals. Not banks. Not retailers. Lawyers.
And the attacks have evolved. Fast.
Ransomware used to mean locked files and a payment demand. That was bad enough. Now attackers run “triple-extortion” campaigns: they encrypt your systems, leak confidential documents online, and then go after your clients directly. Sometimes they even contact opposing counsel just to create chaos.
The financial damage is staggering. The average legal data breach now exceeds $5 million when you factor in downtime, legal exposure, reputational harm, and regulatory fallout.
So here’s the blunt truth: if your firm still treats IT support as a break-fix service—the guy who shows up when Outlook stops working—you’re already behind.
In 2026, your Managed Service Provider (MSP) has to function as a full-scale security partner. Not optional. Essential.
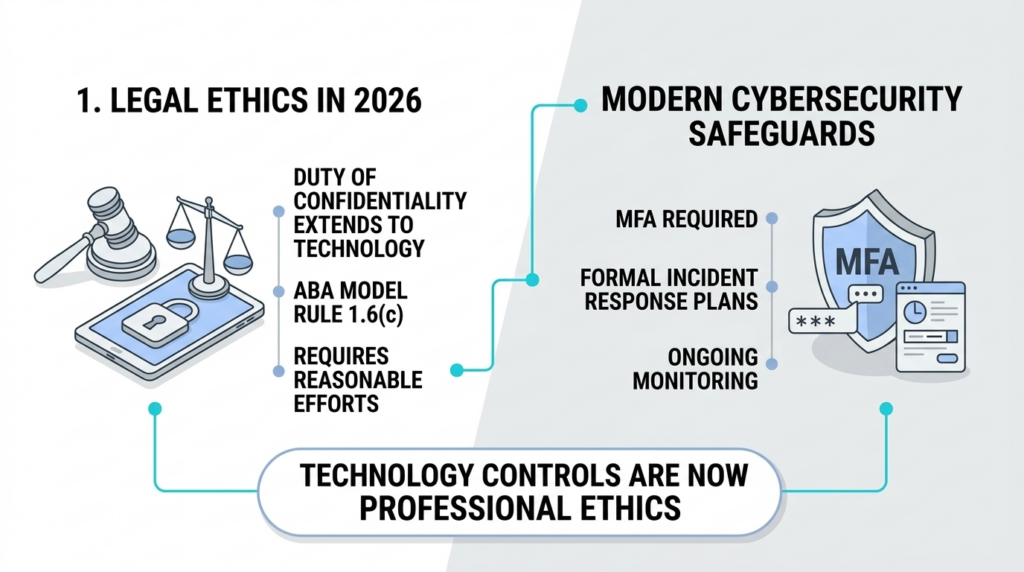
Why Cybersecurity Is Now a Professional Duty for Lawyers
Lawyers already know the phrase “duty of confidentiality.” It’s embedded in legal ethics.
What many firms underestimate is how that duty now intersects with technology.
Under ABA Model Rule 1.6(c), attorneys must make reasonable efforts to protect client information. Ten years ago, that might have meant basic password policies and encrypted laptops.
That bar has moved.
State bar associations increasingly interpret “reasonable efforts” as requiring modern cybersecurity safeguards. Multi-factor authentication. encrypted data systems. monitored access logs. formal incident response plans.
In other words, technical controls are now part of legal ethics.
If a breach exposes client documents and investigators discover that the firm relied on outdated security practices, the issue isn’t just IT failure. It can become a professional responsibility problem.
That’s where a specialized MSP comes in.
Matter-Level Encryption: The Security Standard Law Firms Need
Most businesses rely on full-disk encryption. It protects data stored on a device, which is useful—but limited.
Law firms deal with something far more complex: thousands of separate cases, each with its own confidentiality boundaries.
Modern legal-focused MSPs now deploy matter-level encryption, a security architecture designed specifically for legal environments.
Instead of encrypting an entire system uniformly, the platform encrypts data based on the specific case or “matter.”
Why does that matter?
Because access becomes extremely granular.
Internal Protection
Even if someone inside the firm accidentally gains access to the wrong system folder—or an employee account gets compromised—the attacker still cannot open files belonging to other matters.
The encryption key simply won’t allow it.
External Breach Protection
If hackers manage to exfiltrate documents from the system, those files remain encrypted outside the firm’s network.
Without the corresponding matter-level key, the stolen data is essentially useless.
Audit and Compliance
Law firms increasingly face cyber insurance audits and malpractice investigations following breaches. Matter-level systems maintain detailed logs showing:
- who accessed a file
- when it happened
- which matter it belonged to
That audit trail becomes critical evidence that the firm took reasonable steps to protect client data.
Cyber Attacks Don’t Respect Office Hours
Here’s something many firms still underestimate: cyberattacks almost never happen during business hours.
They happen at 2:00 AM.
Or on a Saturday.
Or during a holiday weekend when no one is watching.
That’s exactly why modern law firm cybersecurity relies on 24/7 monitoring.
The Role of a Managed Security Operations Center (SOC)
A reputable MSP serving legal clients typically includes a Managed Security Operations Center, or SOC.
Think of it as a digital watchtower.
Security analysts continuously monitor your firm’s systems looking for suspicious behavior—patterns that indicate something is wrong.
For example:
- a user downloading thousands of documents in minutes
- a login attempt from another country
- a sudden spike in network activity from a workstation
- privileged access requests at unusual hours
These anomalies trigger alerts instantly.
A trained security team investigates in real time. If necessary, they isolate devices, block access, or shut down compromised accounts before attackers gain control.
That speed matters.
The “exploit gap”—the time between discovering a vulnerability and attackers exploiting it—has shrunk to hours. Sometimes less.
Waiting until Monday morning to review a help desk ticket simply isn’t acceptable anymore.
Backups Alone Won’t Stop Modern Ransomware
Traditional backups used to be the safety net.
If ransomware locked your systems, you restored from backup and moved on.
Attackers adapted.
Modern ransomware groups actively search for backup systems before launching their attack. If they find them, they delete or encrypt them first. Then they deploy ransomware.
No backups. No recovery.
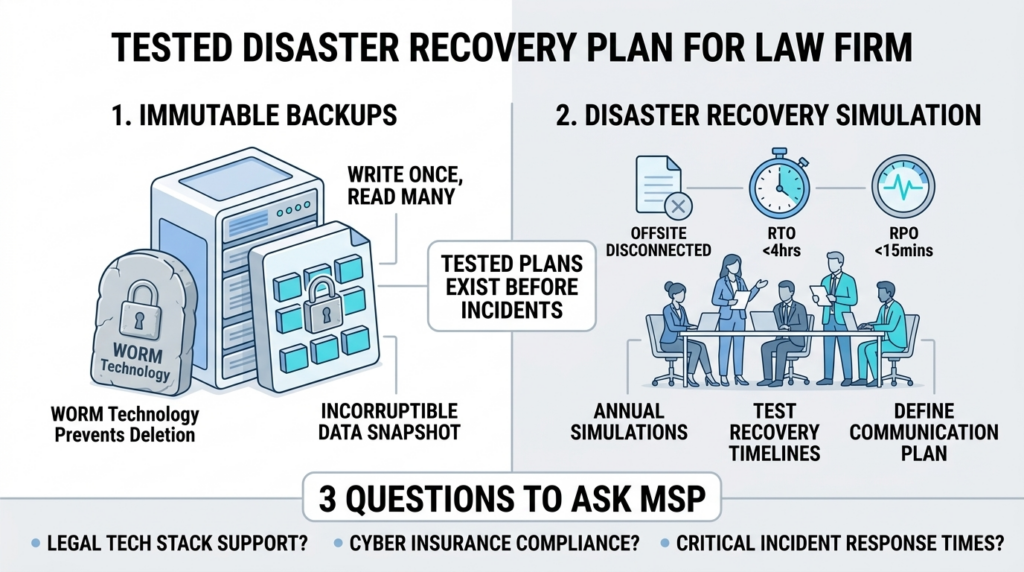
That’s why security standards for law firms now emphasize immutable backups.
What Immutable Backups Actually Do
An immutable backup works on a simple principle: Write Once, Read Many (WORM).
Once data is written into the backup system, it cannot be altered or deleted during the retention period.
Not by hackers.
Not by ransomware.
Not even by administrators.
If attackers infiltrate the network and attempt to erase backup data, the system refuses the command. The snapshot remains intact.
When a firm needs to recover, the data is still there—clean, unmodified, and usable.
Every Law Firm Needs a Tested Disaster Recovery Plan
Backup technology alone isn’t enough. Firms also need a clear recovery strategy.
Experienced MSPs run annual disaster recovery simulations to test whether the firm could actually survive a cyber incident.
These exercises answer uncomfortable but necessary questions.
For example:
Is there an off-site copy of critical data? A properly designed system stores at least one backup copy disconnected from the main network.
How fast can operations resume? The Recovery Time Objective (RTO) determines how quickly systems must be restored. Many firms target four hours or less.
How much data loss is acceptable? The Recovery Point Objective (RPO) measures backup frequency. Modern legal environments often require snapshots every 15 minutes.
Who communicates with clients? When systems go down, someone must notify affected clients, courts, and insurers.
These plans need to exist before an incident occurs—not during it.

Three Questions Every Law Firm Should Ask an MSP
Not every IT provider understands the legal industry. Some MSPs focus on retail or manufacturing environments and simply apply the same tools to law firms.
That approach rarely works.
When evaluating managed IT services for attorneys, ask these questions early.
- Do You Support Our Legal Technology Stack?
Law firms rely on specialized platforms that require careful configuration.
Examples include:
- Clio
- Relativity
- NetDocuments
- iManage
These systems integrate with document management, billing, and case management workflows. Security controls must work seamlessly across all of them.
An MSP unfamiliar with these platforms can break integrations or create compliance gaps without realizing it.
Experience matters here.
- Can You Support Cyber Insurance Requirements?
Cyber insurance providers have tightened their standards dramatically.
Policies often require proof that firms maintain specific security controls—multi-factor authentication, continuous monitoring, formal audits.
Insurers may also request compliance documentation such as SOC 2 Type II reports or security assessments.
If your MSP cannot provide those reports, your firm may face higher premiums—or worse, denied claims after a breach.
- What Are Your Response Times for Critical Incidents?
Service Level Agreements reveal a lot about how seriously an MSP treats security.
Legal-focused providers typically structure response times by severity level.
For example:
- Critical incidents (entire firm offline or confirmed breach) require response in minutes.
- High-priority issues affecting a practice group should be addressed within an hour.
- Standard support requests can follow slower timelines.
The key point: when a cyber incident occurs, speed determines whether the damage stays contained or spirals into a crisis.
Cybersecurity Is Becoming a Competitive Advantage for Law Firms
Something interesting is happening across the legal industry.
Large corporate clients are starting to audit the cybersecurity practices of outside counsel before awarding major engagements.
It makes sense. Companies don’t want confidential business strategies exposed because a law firm used outdated IT systems.
As a result, firms with strong security infrastructure gain a real advantage during client selection.
Being able to demonstrate encrypted document systems, continuous monitoring, and secure cloud backups signals professionalism and reliability.
Clients notice that.
The Bottom Line
Law firm cybersecurity has moved far beyond antivirus software and firewalls.
Today’s threat landscape demands continuous monitoring, encrypted document environments, immutable backups, and rapid incident response.
That level of protection requires expertise most firms don’t maintain internally.
A capable Managed Service Provider fills that gap. They become the technical backbone protecting client data, attorney communications, and the firm’s reputation.
And in 2026, reputation might be the most valuable asset a law firm has.
Lose client trust once—especially after a breach—and rebuilding it can take years.
Choosing the right MSP is no longer an IT decision.
It’s a strategic one.
